Pioneering Virtual Reality and Augmented Reality Solutions
We leverage technology to drive innovation, increase industrial efficiency, revolutionize education and corporate training and showcase products in new ways
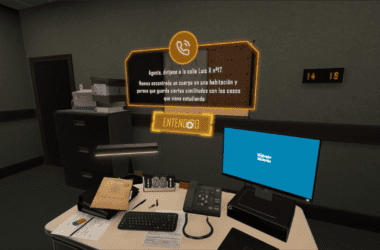
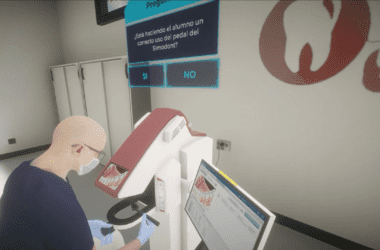
Training with Virtual Reality
Through immersive experiences, we enhance the training of professionals and students across a wide range of environments.
We develop highly realistic simulators and provide a centralized management system (SAVI) for monitoring and evaluation. Our catalog includes simulators on various topics, such as workplace safety, operation of industrial machinery, energy facility management, etc.
Virtual Reality improves knowledge retention, allows learning at a personalised pace and eliminates risks through interactive, hands-on training.

Digitalization of technical operations
Turn any technician into an expert of your company’s critical operations with our SAAM and ATR tools.
We simplify the digitization of technical knowledge using process-driven guidance with videos, 3D animations, real-time data and Augmented Reality.
Our tools provide technicians with instant access to key information in a visual and interactive way.
With our advanced Augmented Reality-based telecare system, field technicians can connect with experts in real time, anytime and anywhere.
Maximise your organization´s efficiency by standardizing technical operations, reducing intervention times and minimizing errors.
Multi-user Virtual Environments
We create collaborative virtual environments where multiple users can interact and work together, either from the same physical location or remotely.
Our solutions support both immersive and non-immersive experiences, optimizing real-time collaboration. These environments remove geographical barriers, reduce travel costs and provide access to equipment and machinery information without the need for a physical version.
They foster innovative and dynamic knowledge sharing, transforming the way teams collaborate and learn.

Are you looking for a partner to develop a custom Augmented reality or Virtual Reality project?
Get in touch and we will find the best solution for your needs.
Technologies
VR headsets, immersive content and AI-driven algorithms are transforming the way people access and interact with information.

Virtual Reality

Augmented Reality

Artificial Intelligence
Sectors
Education and Training
Virtual Reality is transforming education and corporate training delivering faster more hands-on learning than traditional methods.
In educational institutions and workplaces alike, VR lets users safely practice complex or hazardous procedures and operate machinery and equipment that isn’t physically available in their training centers.
This immersive approach enhances technical skills and prepares students and employees for the workforce, making training safer, more engaging and more effective.
Industry 4.0
Virtual Reality, Augmented Reality and Artificial Intelligence are driving digital transformation in Industry 4.0.
These tools not only optimize training and improve accuracy in increasingly complex production processes, but also support predictive and corrective maintenance of equipment, enabling operators to perform diagnostics and repairs more efficiently and safely
Marketing and Sales
Virtual and Augmented reality bring significant value to marketing and sales by enhancing presentation, capturing the attention of potential clients and helping them better understand your products.
The technologies enable the creation of interactive experiences and immersive marketing campaigns that increase impact and improve message retention.